What is Internet Phishing? How email hacking is done?
In today’s world, computer systems and networks are heavily defended against attackers. They find it extremely difficult and time consuming to directly hack the system.
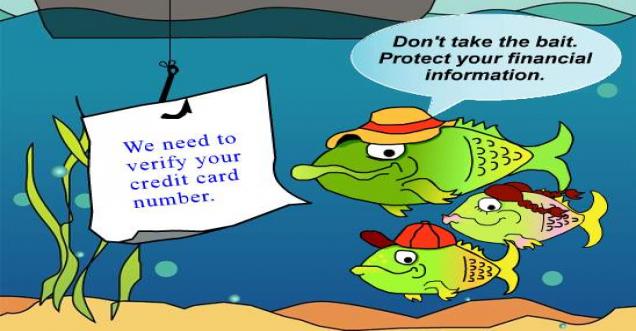
To overcome this issue, they simply go around it by attacking the end user and not the computer systems. Reason being, the end users are the one who really has details to hack to the computer systems. The end user has – network, username, password, and a computer that is behind the network firewall which can possibly provide access to your company or home computer system. Internet phishing is the process through which hackers enters your system, when you click on the link sent by them. This is also known as email hacking.
How Phishing is done?
Phishers are the people who have expertise in fooling you by creating a fake email account. It might seem that the mail account is from some person you might know and trust. It could be from the bank in which you have account, credit card or some top web sites. They send mail to you to confirm your account details by clicking on the link that they send in the mail. On clicking it might redirect to the website similar to the actual website. And here comes the trap, if you enter your details, then these phishers get access of your personal data. They can use it to make actual purchases online.
To protect yourself:
- Remember that your bank or any re-known company will never ask for your personal details.
- They never send messages life “WARNING” or threaten to close your account if you don’t respond immediately.
- If the received mail don’t address you by your name, or if they have some spelling mistakes, or if they don’t look professional, try to avoid it. For example, you might receive a mail from Microsoft that it requires you to authenticate your windows. The user id could be like John@gmail.com. Remember, if Microsoft sends you mail then the mail id of the sender should have Microsoft in its email id. John@microsoft.com can be the correct id.
- You can hover over the link in the email messages and on websites to verify the link’s actual destination. If the link says that click here to visit our website Microsoft.com. Then if you hover your mouse over the link, then at the bottom of the page you can see the actual URL in which it will redirect you once you click on that.
- The best way to identify a fake URL is by watching the first word ending after https://. This is the domain name. You should ignore the subdomain, folder and page names.
- The best practices advice that if you want to login to your banking website then go directly through the website name, instead of using link from your mail. For example. Anyone can create pages such as – http://www.zyz.com/mircosoft/authentication/windowCheck.aspx. So the folder Microsoft should not confuse you.
- If the site that you are clicking has https. It ensures that the website that you are visiting uses encryption. So check for urls which has https in it.
- You should remember that phishing emails are not always intended to steal your information. It might install some software (by running some shell scripts) and it can start monitoring your keystrokes and can even take full control of your computer.
- Whenever you see some suspicious mail in your mail box, make sure to mark it as spam.
- Phishing can also happen through SMS text messages, faxes and even through automated voice response systems.
- So you should never trust phone numbers found in suspicious email messages, even if an authentic sounding voice response system answers. Instead, use the phone number found on your card or statements.
TO SAVE YOURSELF FROM INTERNET PHISHING, THINK BEFORE YOU CLICK. A WRONG CLICK CAN DEVASTATE YOUR PERSONAL INFORMATION.











.jpg)














